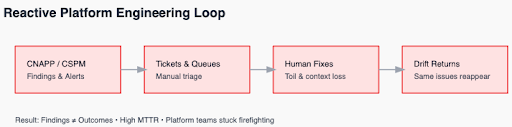
Platform engineering teams face a growing paradox: we’ve never had more visibility into infrastructure risk, yet we still spend an enormous portion of our time in reactive firefighting.
Security alerts, CSPM findings, CNAPP dashboards, and audit tickets constantly surface issues. But visibility alone doesn’t create outcomes. These tools tell you something is wrong — not how to fix it at scale. Instead, teams end up chasing alerts, triaging findings, and closing tickets.
As infrastructure change velocity skyrockets due to AI-assisted development, the gap between detection and remediation continues to widen.
The Limits of CNAPP and CSPM Alert-Based Security
At scale, the core issue is simple: finding problems isn’t the same as fixing them. Tools like CNAPP and CSPM scan environments and generate alerts, but those alerts quickly turn into backlogs of manual work.
Each finding becomes a ticket, a context switch, or a late-night investigation. This human-in-the-loop model assumes engineers have unlimited time and perfect context — neither of which is true.
Reactive security tools are strong at detection but weak at:
- Contextual prioritization
- Actionable remediation guidance
- Integration with GitOps and CI/CD workflows
The answer isn’t fewer alerts — it’s making findings matter.
Platform teams must shift from:
Find → Ticket → Fix
to:
Detect → Understand → Remediate
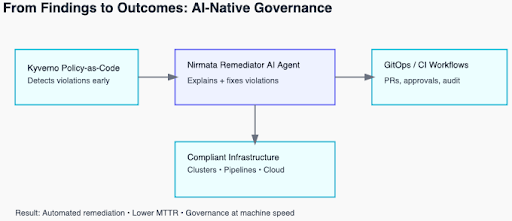
This is where policy as code and AI-driven automation change the model. Encoding standards as executable policies ensures infrastructure is evaluated consistently across Kubernetes, CI/CD, and infrastructure-as-code environments.
But detection alone isn’t enough. Teams need automated, context-aware remediation that turns violations into fixes — ideally delivered through pull requests and existing workflows rather than more dashboards.
That’s how platform engineering moves from reactive firefighting to proactive governance.
From Alert to Action: The Remediator AI Agent
To close the loop between detection and resolution, Nirmata’s Remediator AI Agent transforms passive findings into actionable remediation workflows. Instead of surfacing a policy violation and leaving a human to research and fix it, Remediator continuously detects violations from Kyverno, interprets them with AI, and proposes or implements fixes. It can even open Pull Requests in GitOps workflows with context-aware diffs and explanations of what changed and why.
The Remediator Agent goes beyond static alerts in 3 ways:
- Continuous Detection: It monitors fleet-wide policy violations in real-time, eliminating long waits for batch scans.
- Contextual Understanding: AI interprets both the violation and the larger infrastructure context to produce precise remediation actions. No guesswork.
- GitOps Integration: Fixes aren’t applied silently; they flow through your existing approval workflows as pull requests, preserving compliance and auditability.
The outcome is that platform engineers spend less time interpreting noise and more time on strategic governance, security, and platform design.
Why Reactive Mode Breaks Platform Teams
Reactive tooling locks platform teams into a treadmill where findings generate tickets, and tickets generate more manual work. This approach assumes that humans are the deciding factor for every remedial step, but as infrastructure movement accelerates, especially with AI-driven code and config generation, that assumption breaks. Teams simply do not have the time, context, or cognitive capacity to process every alert manually. The result is:
- Delayed MTTR (mean time to remediation) because humans are the slowest part of the workflow.
- Inefficient resource allocation, where engineers fix noisy alerts instead of high-impact issues.
- Context gaps, because tickets strip out or obscure relevant state (e.g., dependencies, platform policies, deployment history).
What platform engineering really needs isn’t more alerts but meaningful, prioritized, and automated resolution paths.
Building a Proactive Platform Workflow
To break out of reactive mode, modern platforms must embrace 3 pillars:
- Executable Guardrails: Policies as code with clear intent that can be enforced consistently at development, build, deploy, and runtime stages.
- Context-Aware Remediation: AI-driven fixes that propose or apply remediation actions with clear explanations and audit trails.
- Workflow Integration: Preserving the tools and processes teams already use, GitOps pipelines, pull requests, CI/CD – to ensure fixes don’t bypass governance.
Together, these pillars create a closed-loop system where findings result in action, not backlog.
Take the example of a policy violation for missing resource limits. Under a reactive model, this yields an alert, a ticket, a manual edit in YAML, and another deployment cycle. With Nirmata’s flow, the violation is detected, contextualized, and a pull request with a compliant patch is generated automatically, the human only needs to review and merge. This is far more scalable and far less costly in terms of engineer hours.
Beyond Alerts: Measuring Outcomes
A core measure of success is not “how many violations were found,” but “how many were resolved with minimal human overhead.” With automated remediation that respects policy guardrails and workflow approvals, MTTR drops from days to minutes. Engineers regain focus on strategic projects instead of manual triage, and developers experience fewer blocked deployments because issues are resolved upstream. Platforms become enablers, not bottlenecks.
Ready to move from reactive firefighting to scalable, AI-speed governance? See how platform teams are building paved roads instead of speed bumps with Kyverno and Nirmata.