Kyverno sits in a unique and critical position in a Kubernetes platform. It isn’t just another controller running in the cluster, it’s part of the admission control path. Every deployment, every update, and every policy decision depends on Kyverno being healthy, performant, and correctly configured.
That’s why simply running Kyverno isn’t enough. Platform teams need to know:
- Is Kyverno healthy?
- Is it configured correctly for production?
- And will it scale as our clusters and workloads grow?
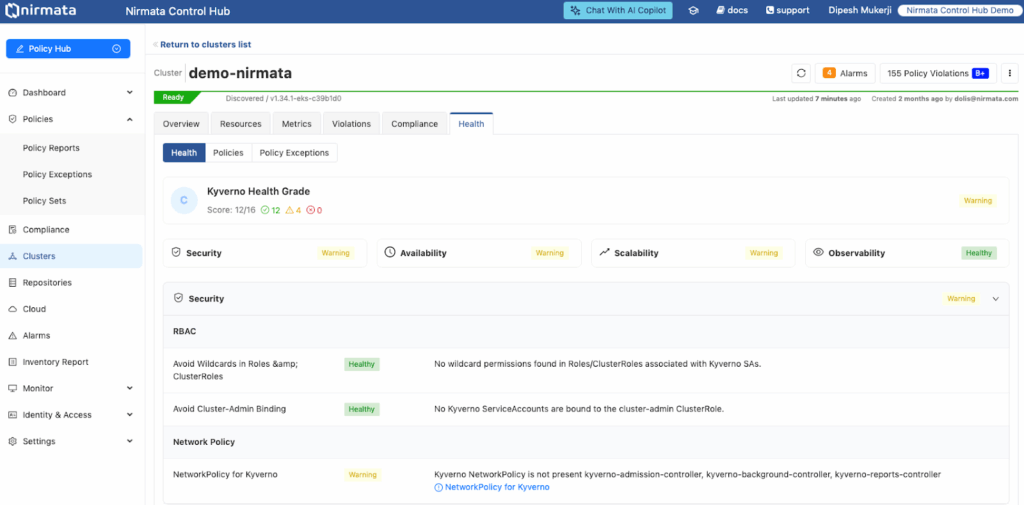
This is exactly the problem the Kyverno Health Check and Reporting feature in the Nirmata Control Hub is designed to solve.
Making Kyverno Operationally Safe at Scale
The Kyverno Health Check is not about policy violations, you already have reports for that. Instead, it focuses on something even more foundational: the health and operational readiness of Kyverno itself.
The feature continuously evaluates Kyverno across 4 critical dimensions:
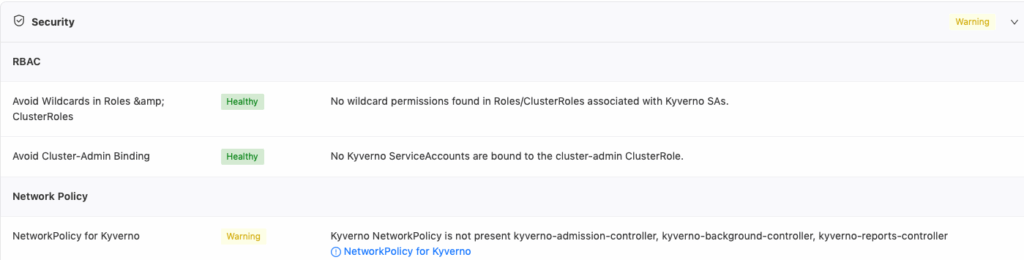
Security
Kyverno Health Checks validate that Kyverno is running with least-privilege access, not excessive permissions that increase blast radius. It flags risky RBAC configurations (such as wildcard permissions), ensures Kyverno isn’t bound to cluster-admin, and verifies that proper NetworkPolicies are in place to protect the admission webhook.
In short, it answers the question:
Is our policy engine secure enough to be trusted in production?
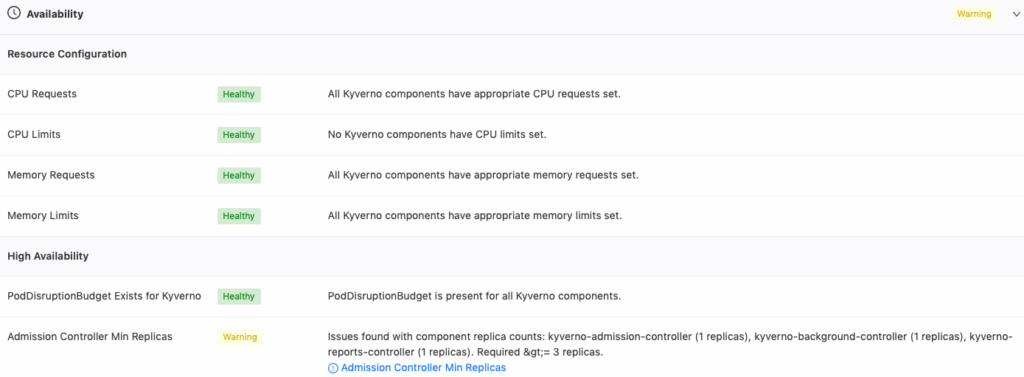
Availability
Because Kyverno runs in the critical path, availability is non-negotiable. The Health Check evaluates:
- CPU and memory requests and limits
- Pod restarts and OOMKills
- Replica counts and PodDisruptionBudgets
- Whether Kyverno can survive node failures, upgrades, and load spikes
This helps platform engineers detect issues before they turn into blocked deployments or failed admission requests.
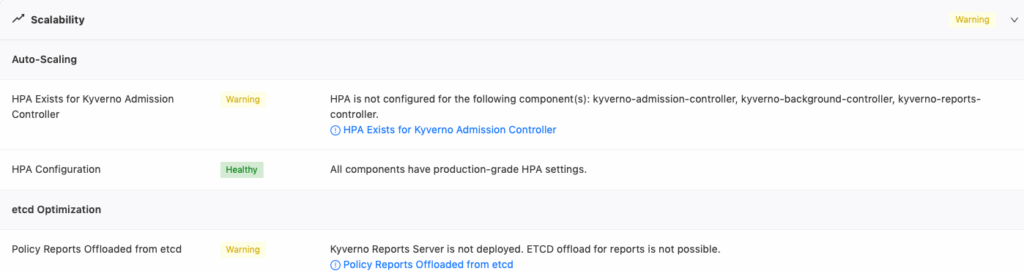
Scalability
As clusters grow, Kyverno must scale with them. The Health Check examines:
- Horizontal Pod Autoscaler (HPA) configuration
- Admission webhook latency and timeout settings
- Etcd offload configuration for reports
- Unused controllers that waste resources
Instead of guessing whether Kyverno is “tuned well enough,” teams get concrete recommendations based on real usage and best practices.
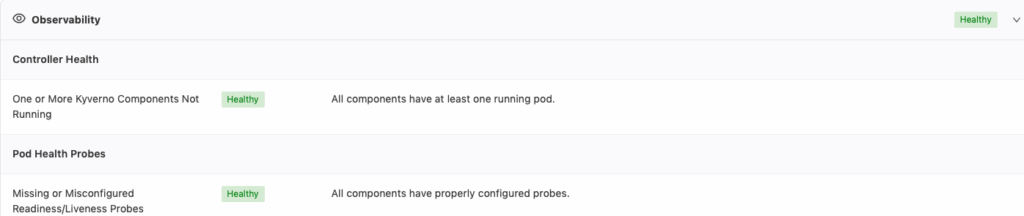
Observability
Finally, the Health Check looks beyond static configuration:
- Pod readiness and liveness
- Policy readiness and error states
- Controller logs for panics, fatal errors, and admission failures
- Metrics trends over time (CPU, memory, request volume)
This gives teams a clear, graded view of Kyverno health, not just raw metrics that require interpretation.
Who the Kyverno Health Check Is For
The Kyverno Health Check is built specifically for platform engineers and security administrators who are responsible for Kubernetes reliability and governance at scale.
- Platform Engineers – use it to ensure Kyverno is production-ready, resilient, and properly sized across environments.
- Security Teams – rely on it to detect misconfigurations, tampering risks, and policy engine instability before they become security incidents.
- SREs and Operations Teams – benefit from early warnings and remediation guidance instead of reactive firefighting.
It’s especially valuable for teams running multi-cluster or multi-cloud environments, where inconsistencies and drift are otherwise hard to spot.
Why This Matters to Platform Engineers
From a platform engineer’s perspective, Kyverno health is not an abstract concern. When Kyverno is misconfigured or unstable, the consequences are immediate and painful:
- Deployments get blocked unexpectedly
- Admission requests time out
- Policies fail silently or stop enforcing
- Engineers lose trust in the platform
The Kyverno Health Check shifts teams from reactive troubleshooting to proactive confidence. It surfaces issues early, explains why they matter, and provides remediation guidance so engineers can act quickly and decisively.
Equally important, the Health Check is available:
- During cluster onboarding, to prevent bad configurations from reaching production
- Periodically, to detect drift and degradation over time
- On-demand, when teams need immediate insight
This turns Kyverno from a “black box in the control plane” into a well-understood, observable system.
The Value of Kyverno Health Check in NCH
Most Kubernetes monitoring tools focus on infrastructure health, such as nodes, pods, and clusters. Some policy tools focus only on policy violations. Nirmata’s Kyverno Health Check is different because it focuses on the policy engine itself.
Policy-Aware, Not Just Metrics-Aware
Instead of showing raw CPU or memory charts, the Health Check understands what Kyverno is supposed to be doing and whether it can safely do it. It connects configuration, metrics, and policy behavior into a single operational view.
Opinionated Best Practices, Not Just Signals
This isn’t a generic dashboard. The Health Check encodes Kyverno production best practices – replica counts, RBAC scoping, webhook tuning, controller usage, and tells you when your setup deviates from what works at scale.
Built for Platform Governance, Not Just Observability
The feature integrates directly into the Nirmata Control Hub, giving teams centralized visibility across clusters. It’s designed for governance and operational excellence, not just alerting noise.
Actionable by Design
Perhaps most importantly, the Kyverno Health Check doesn’t just say something is wrong. It explains:
- Why it matters
- What the risk is
- What to do next
This makes it far more valuable than dashboards that leave platform teams to connect the dots themselves.
Power Without Confidence is Fragile
Kyverno is powerful, but power without confidence is fragile. The Kyverno Health Check in Nirmata Control Hub gives platform engineers the assurance that their policy engine is secure, available, scalable, and observable, even as their environments grow more complex.
For teams that rely on policy-as-code to keep Kubernetes safe and compliant, Kyverno Health Checks aren’t a nice-to-have, they’re a prerequisite for running policy in production with confidence.