This document provides an overview of Nirmata’s security policies and practices. For more information, questions, and to report any security issues please contact security@nirmata.com.
Security is an essential part of our business
The Nirmata team is vested in the establishment and maintenance of security best practices. Our security policies and architectures have been developed with consultation and from cloud provider partners, like Amazon Web Services, as well as security solution providers in the Cloud Native Computing Foundation (CNCF) ecosystem. Our philosophy is “secure by default” to ensure that security is not an afterthought but is built-in.
Product Security
Delivery Models
The Nirmata Cloud Edition offers a Software-as-a-Service (SaaS) delivery model, while the Nirmata Private Edition enables Nirmata to be downloaded and installed in your data center or cloud.
Both editions of the Nirmata solutions have the same security architecture. The only difference is whether Nirmata is managed by our global operations team, or by our customers operations team.
Architecture
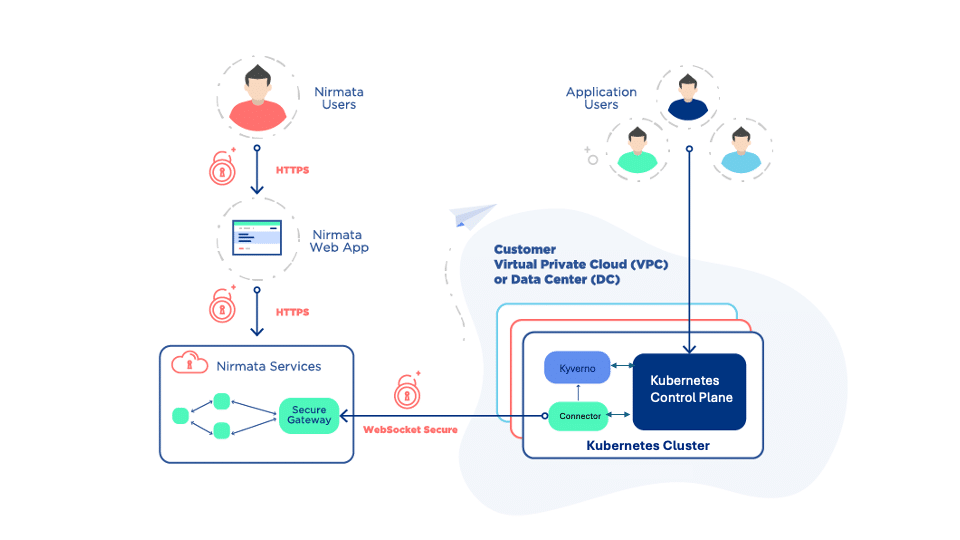
Nirmata is designed to have zero access or visibility to your application data. Nirmata is architected so that your applications can run on your secure servers in your Virtual Private Cloud (VPC) or Data Center (DC).
The Nirmata Connector is a secure static container that runs on each Kubernetes cluster. The connector is single-homed to connect only to the Nirmata services (e.g. nirmata.io) using WebSocket Secure (WSS) protocol. The Nirmata Connector is designed to adhere to CIS Benchmarks for container security, and our Customer Success team has extensive experience with assisting your operations and security teams in establishing security best practices for Kubernetes Clusters.
Data Access
The Nirmata Web Application, and other clients like the REST API and CLI, access Nirmata services using HTTP over SSL (HTTPS).
Nirmata retrieves and stores policy-related information such as policies, policy violations, and policy exceptions. Additionally, it retrieves Kubernetes resource metadata to correlate policy violations to resources and for remediation.
Data Encryption
Nirmata encrypts all sensitive customer data, such as access tokens or passwords. Nirmata staff members do not have the ability to decrypt encrypted customer data.
All Nirmata inter-service communications are encrypted using SSL. Each Nirmata service has a unique identify managed by a X.509 certificate. Communication across services is authenticated using the public-private keys and HMAC (hash-based message authentication code) and access control permissions are applied.
Secure Data Centers
The Nirmata Cloud Edition SaaS runs on secure Amazon Web Services (AWS) data centers that have achieved ISO 27001 certification, PCI DSS Level 1 compliance, and SAS70 Type II. As an AWS partner and an official solution provider to Amazon Web Services, Nirmata abides by AWS security best practices and well-architected framework. Nirmata has successfully completed AWS Foundational Technical Review (FTR). In addition, Nirmata has achieved SOC-2 Type 2 compliance.
Security Features
In addition to being built with a secure architecture, Nirmata also applies security best practices to Kubernetes clusters and workloads. The following is a list of the major security related features that Nirmata enables. For complete details please review the Nirmata customer documentation.
Single Sign On
Nirmata integrates with your Active Directory Federation Services (ADFS) or any other SAML v2 Identity Provider (IdP) to enable Single Sign On (SSO) for users.
Role Based Access Controls
Nirmata uses Role Base Access Controls for user and team authorization. This ensures that users get appropriate level of access based on their role and responsibilities.
Network Policies
Nirmata makes it easy to configure and manage Kubernetes Network Policies that allow network traffic microsegmentation. Cluster Multitenancy and Microsegmentation are highly recommended and can be easily enforced using Nirmata.
Multi-Factor Authentication
Nirmata allows requiring multi-factor authentication for securing access to the Nirmata Web Console.
Kubernetes Security
Nirmata enables several security and operational best practices for Kubernetes.
Partner Integrations
Nirmata has deep integrations and partnerships with leading container security and management solutions. To see a complete list of Nirmata ecosystem partners, you can visit our partner page.
Additional Information
You can find additional information on the Nirmata product in our customer documentation. For more information, or if you would like to further discuss our approach to security, please feel free to contact us to setup a time for a deep-dive discussion with our team.

